Researchers are warning of threat actors increasingly abusing the Cloudflare Tunnel service in malware campaigns that usually deliver remote access trojans (RATs).
This cybercriminal activity was frst detected in February and it is leveraging the TryCloudflare free service to distribute multiple RATs, including AsyncRAT, GuLoader, VenomRAT, Remcos RAT, and Xworm.
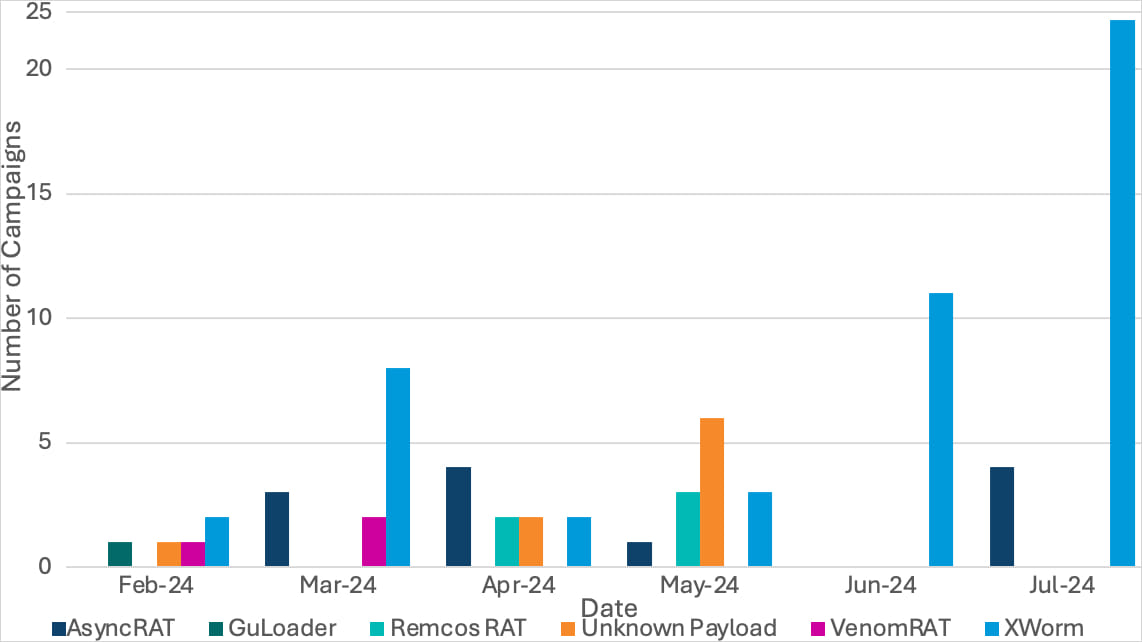
Source: Proofpoint
The Cloudflare Tunnel service allows proxying traffic through an encrypted tunnel to access local services and servers over the internet without exposing IP addresses. This should come with added security and convenience because there is no need to open any public inbound ports or to set up VPN connections.
With TryCloudflare, users can create temporary tunnels to local servers and test the service without the need of a Cloudflare account.
Each tunnel generates a temporary random subdomain on the trycloudflare.com domain, which is used to route traffic through Cloudflare’s network to the local server.
Threat actors have abused the feature in the past to gain remote access to compromised systems while evading detection.
Latest campaign
In a report today, cybersecurity company Proofpoint says that it observed malware activity targeting law, finance, manufacturing, and technology organizations with malicious .LNK files hosted on the legitimate TryCloudflare domain.
The threat actors are luring targets with tax-themed emails with URLs or attachments leading to the LNK payload. When launched, the payload runs BAT or CMD scripts that deploy PowerShell.
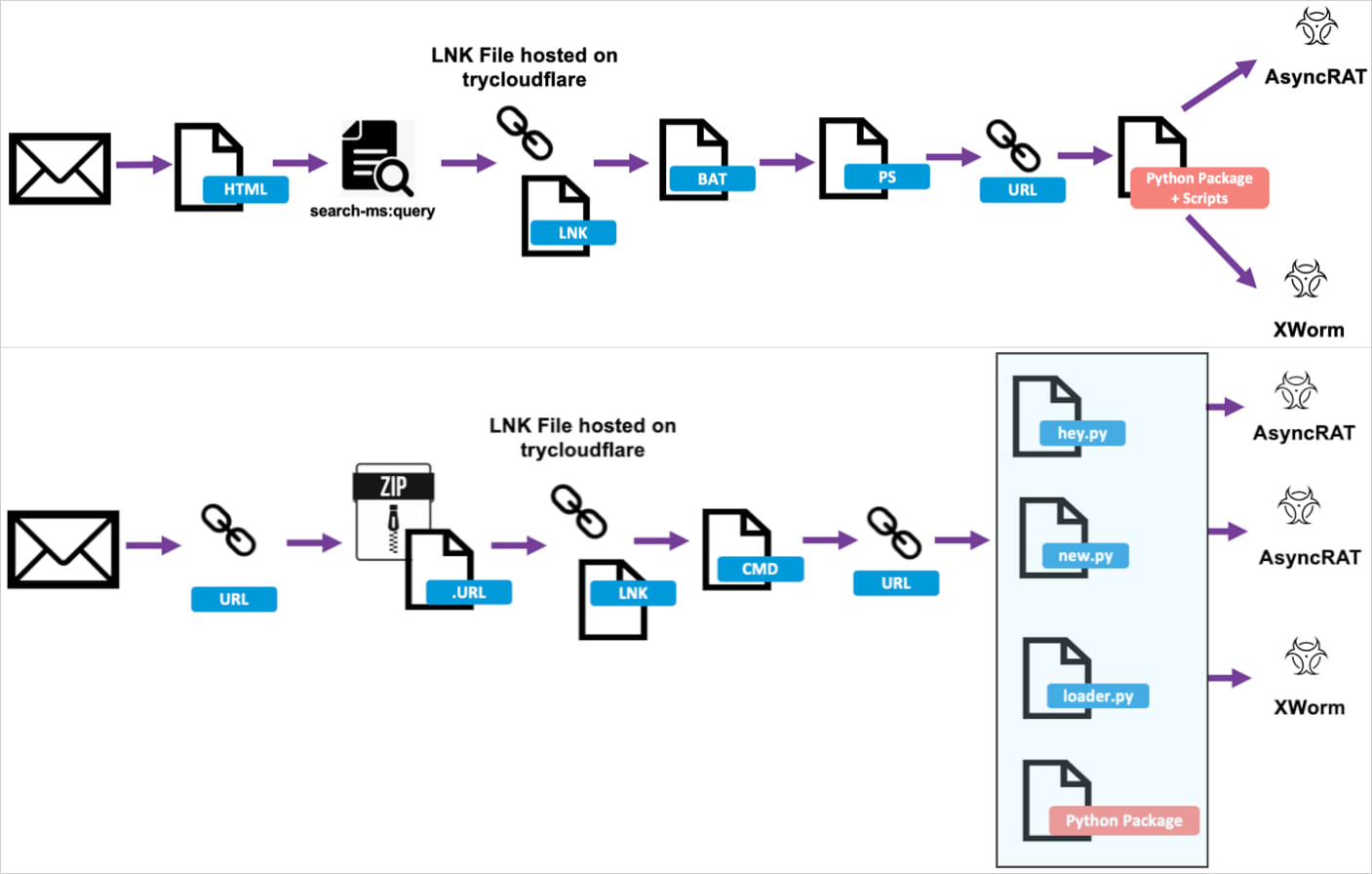
Source: Proofpoint
In the final stage of the attack, Python installers are downloaded for the final payload.
Proofpoint reports that the email distribution wave that started on July 11 has distributed over 1,500 malicious messages, while an earlier wave from May 28 contained less than 50 messages.
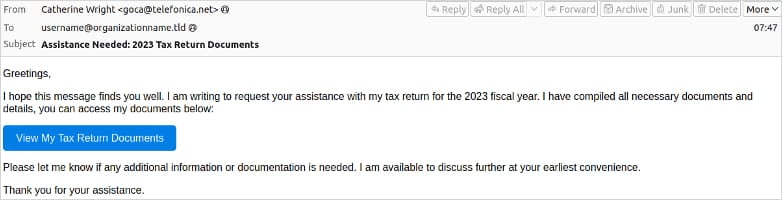
Source: Proofpoint
Hosting LNK files on Cloudflare offers several benefits, including making the traffic appear legitimate due to the service’s reputation.
Moreover, the TryCloudflare Tunnel feature offers anonymity, and the LNK-serving subdomains are temporary, so blocking them does not help defenders too much.
Ultimately, the service is free and reliable, so the cybercriminals do not need to cover the cost of setting up their own infrastructure. If automation is employed to evade blocks from Cloudflare, the cybercriminals can abuse those tunnels even for large-scale operations.
BleepingComputer has reached Cloudflare for a comment on the activity reported by Proofpoint, and a company representative replied with the following statement:
Cloudflare immediately disables and takes down malicious tunnels as they are discovered by our team or reported on by third parties.
In the past few years, Cloudflare has introduced machine learning detections on our tunnel product in order to better contain malicious activity that may occur.
We encourage Proofpoint and other security vendors to submit any suspicious URLs and we will take action against any customers that use our services for malware.
Related Articles:
Malicious PyPi packages create CloudFlare Tunnel to bypass firewalls
Hackers increasingly abuse Cloudflare Tunnel for stealthy connections
Over 3,000 GitHub accounts used by malware distribution service
Fake CrowdStrike repair manual pushes new infostealer malware