A previously undocumented APT group tracked as LilacSquid targeted organizations in the U.S., Europe, and Asia since at least 2021.
Cisco Talos researchers reported that a previously undocumented APT group, tracked as LilacSquid, conducted a data theft campaign since at least 2021.
The attacks targeted entities in multiple industries, including organizations in information technology and industrial sectors in the United States, organizations in the energy sector in Europe, and the pharmaceutical sector in Asia.
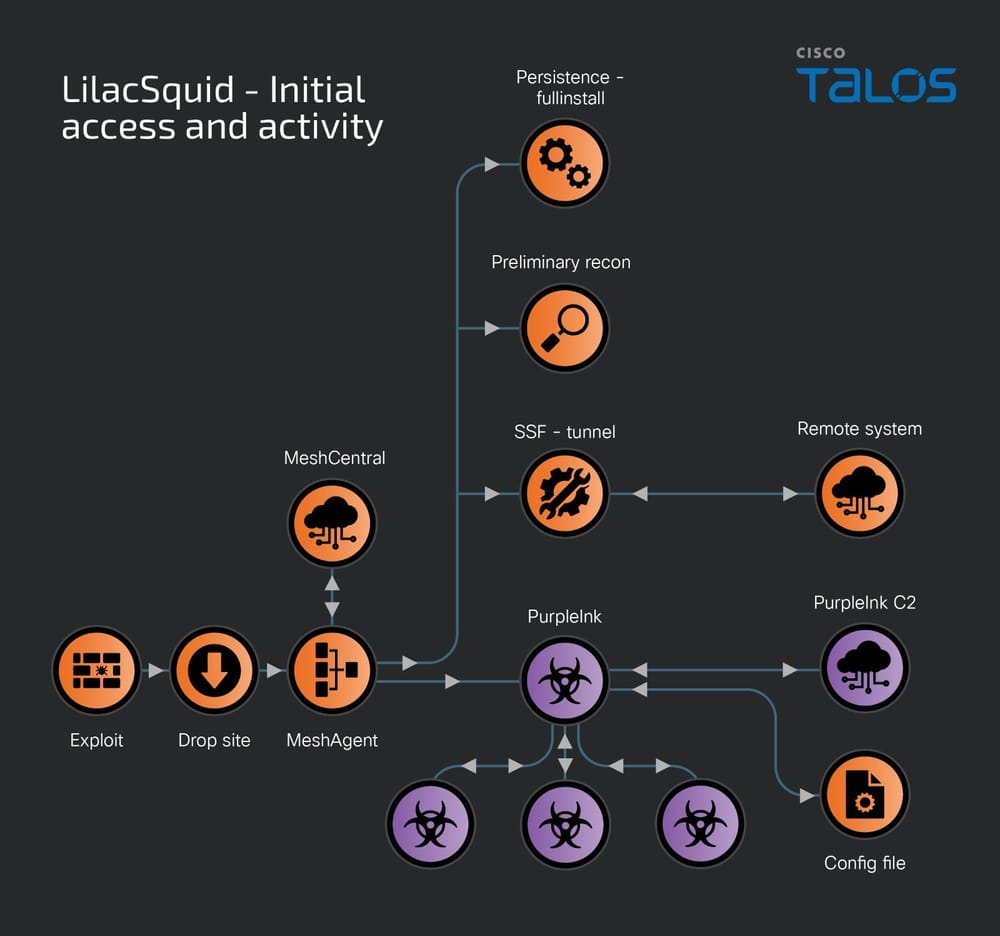
Threat actors were observed using the open-source remote management tool MeshAgent and a customized version of QuasarRAT malware tracked by Talos as PurpleInk.
PurpleInk is the primary implant in post-exploitation activity in attacks aimed at vulnerable application servers.
The attackers exploited vulnerabilities in Internet-facing application servers and compromised remote desktop protocol (RDP) credentials to deploy a variety of open-source tools, including MeshAgent and Secure Socket Funneling (SSF), alongside customized malware, such as “PurpleInk,” and “InkBox” and “InkLoader loaders.” The Secure Socket Funneling (SSF) tool allows attackers to proxy and tunnel multiple sockets through a secure TLS tunnel.
The threat actors aim to establish long-term access to compromised victims’ organizations to steal sensitive data.
The researchers pointed out that LilacSquid’s tactics, techniques, and procedures (TTPs) overlap with North Korea-linked APT groups such as Andariel and Lazarus. The Andariel APT group has been reported using MeshAgent for post-compromise access, while Lazarus extensively uses SOCKs proxy and tunneling tools along with custom malware to maintain persistence and data exfiltration. LilacSquid similarly uses SSF and other malware to create tunnels to their remote servers.

InkLoader is .NET-based loader designed to run a hardcoded executable or command. It supports persistence mechanism and was spotted deploying PurpleInk.
LilacSquid uses InkLoader in conjunction with PurpleInk when they can create and maintain remote desktop (RDP) sessions using stolen credentials. After a successful RDP login, attackers downloaded InkLoader and PurpleInk, copied to specific directories, and InkLoader is registered as a service. The service is used to launch the InkLoader, which in turn deploys PurpleInk.
PurpleInk is actively developed since 2021, it relies on a configuration file to obtain information such as the command and control (C2) server’s address and port, which is typically base64-decoded and decrypted.
PurpleInk is heavily obfuscated and versatile, the malware supports multiple RAT capabilities including:
- Enumerating processes and sending details to the C2.
- Terminating specified processes.
- Running new applications.
- Gathering drive information.
- Enumerating directories and obtaining file details.
- Reading and exfiltrating specified files.
- Replacing or appending content to specified files.
Talos also observed the APT using a custom tool called InkBox to deploy PurpleInk prior to InkLoader.
“InkBox is a malware loader that will read from a hardcoded file path on disk and decrypt its contents. The decrypted content is another executable assembly that is then run by invoking its Entry Point within the InkBox process.” reads the analysis published by Talos.
The researchers provided Indicators of Compromise (IOCs) for the above threats on GitHub.