In a new investigation, The DFIR Report’s Threat Intel Group has shed light on the growing operations of the Fog ransomware group, revealing a sophisticated arsenal of tools and techniques employed to breach networks across multiple industries and geographies.
First observed in mid-2024, Fog has demonstrated a proficiency in reconnaissance, credential theft, privilege escalation, and command-and-control operations. The analysis stemmed from the discovery of an open directory hosted at 194.48.154.79:80, a server likely operated by a Fog affiliate.
“Analysis of its contents revealed a comprehensive toolkit used for reconnaissance, exploitation, credential theft, and command-and-control activities,” the report notes.

The server contained a vast array of offensive tools, including:
- SonicWall Scanner: For exploiting VPN credentials.
- DonPAPI: For extracting Windows DPAPI-protected credentials.
- Certipy: For abusing Active Directory Certificate Services (AD CS).
- Zer0dump and Pachine/noPac: For exploiting Active Directory vulnerabilities like CVE-2020-1472 and CVE-2021-42278/42287.
- Sliver C2: A powerful post-exploitation command-and-control framework.
- AnyDesk: Deployed via a PowerShell script for stealthy persistence with the default password Admin#123.
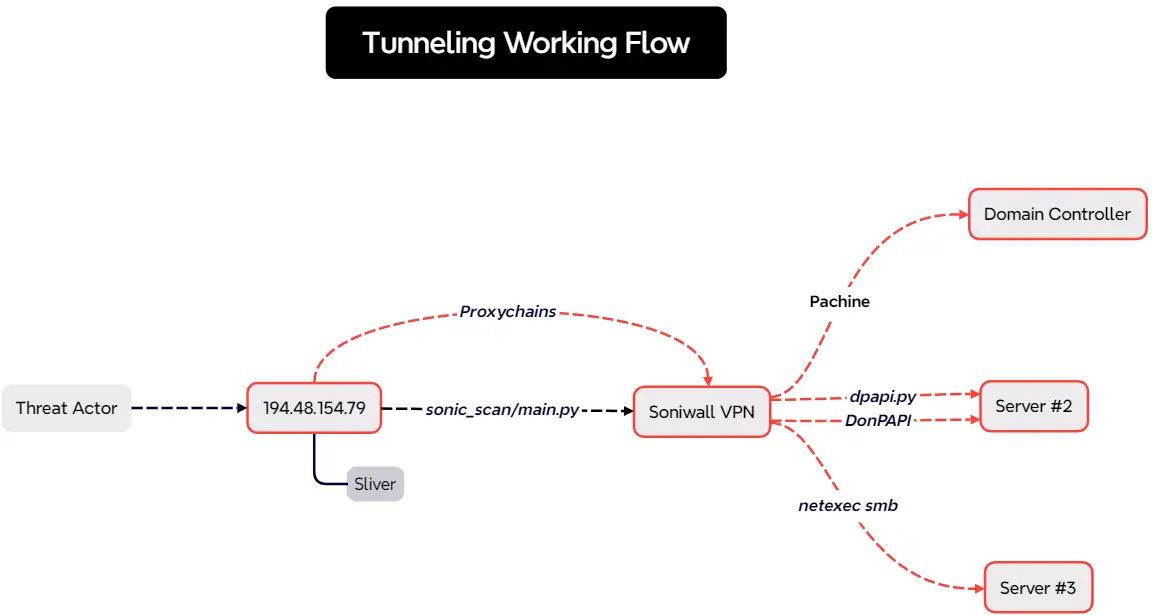
“Proxychains and Powercat were used to facilitate stealthy lateral movement and reverse shells,“ the report explains. The group’s use of Proxychains allowed them to execute commands from the C2 server while leaving minimal traces on compromised endpoints.
Victim data found on the exposed server indicated that Fog targeted organizations in the technology, education, transportation, and retail sectors. Geographically, their operations spanned Italy, Greece, Brazil, and the United States.
The investigation highlighted a specific breach involving ouroverde.net.br, a Brazilian victim whose data appeared on Fog’s Dedicated Leak Site (DLS), confirming the ransomware group’s direct involvement.
Another notable compromise involved the Greek retail group Fourlis, where internal domain artifacts were found on the exposed server, correlating with a contemporaneous public cyberattack disclosure.
Fog’s operations exhibit a layered attack chain:
- Initial Access: Exploiting valid SonicWall VPN credentials using automated scripts.
- Credential Access: Harvesting credentials with DonPAPI and Impacket’s DPAPI modules, and extracting domain backup keys.
- Privilege Escalation: Leveraging Zer0dump and noPac to escalate privileges to domain admin.
- Persistence: Installing AnyDesk silently for continuous access, configured with hardcoded credentials.
- Command-and-Control: Deploying Sliver C2 implants for robust C2 communications, alongside Proxychains and Powercat for stealthy network navigation.
The server hosting the open directory was briefly observed operating a Sliver team server on port 31337 before disappearing from view. Notably, the server was rented through Clouvider (AS62240), a common provider for C2 infrastructure among various threat groups.
“The DFIR Report’s Threat Intel Group assesses with moderate confidence the open directory was used by an affiliate of the Fog ransomware group,” the report concluded.