Searchable Encryption has long been a mystery. An oxymoron. An unattainable dream of cybersecurity professionals everywhere.
Organizations know they must encrypt their most valuable, sensitive data to prevent data theft and breaches. They also understand that organizational data exists to be used. To be searched, viewed, and modified to keep businesses running. Unfortunately, our Network and Data Security Engineers were taught for decades that you just can’t search or edit data while in an encrypted state.
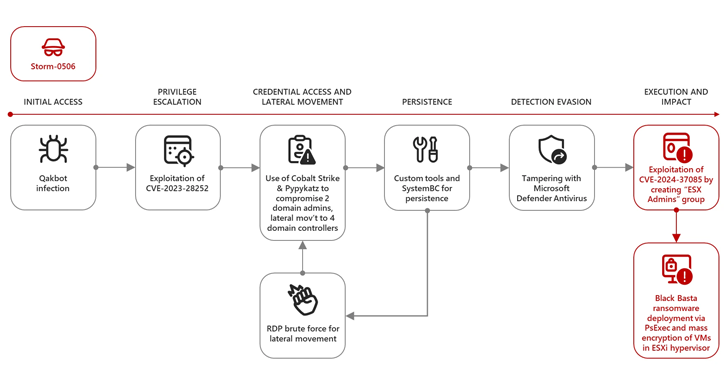
The best they could do was to wrap that plaintext, unencrypted data within a cocoon of complex hardware, software, policies, controls, and governance. And how has that worked to date? Just look at the T-Mobile breach, the United Healthcare breach, Uber, Verizon, Kaiser Foundation Health Plan, Bank of America, Prudential… and the list goes on. All the data that was stolen in those breaches remained unencrypted to support day-to-day operations.
It’s safe to conclude that the way we’re securing that data just isn’t working. It’s critical that we evolve our thought and approach. It’s time to encrypt all data at rest, in transit, and also IN USE. So, how do we effectively encrypt data that needs to be used?
The Encryption Challenge#
As stated, it’s well established that most data is not being encrypted. Just look at the well documented, ongoing growth rate of cybercrime activity. In short, all data breaches and data ransom cases have one glaring common thread— every target maintains millions of private, sensitive, and confidential records in an unencrypted state. Stores of data, fully indexed, structured and unencrypted as easy to read plaintext simply to support operational use cases. This challenge falls under the auspices of “Acceptable Risk”.
It’s often viewed that if an organization has good cyber hygiene, that organization is encrypting data at rest (in storage, archived, or backed up) and in transit or motion (i.e. email encryption, or sending data from one point to another point). And many may think that’s enough—or that is the best they can do. After all, encryption at rest and in motion is the only encryption focus of current compliance and governance bodies, where they address database encryption.
In truth, most compliance lacks any real definition of what would be considered strong database encryption. Unfortunately, the mindset for many is still ‘if compliance doesn’t address it, it must not be that important, right?’
Let’s unpack this a little. Why don’t we encrypt data? Encryption has a reputation for being complex, expensive, and difficult to manage.
Just looking at traditional encryption of data at rest (archives and static data), these encryption solutions commonly involve a complete “lift and shift” of the database to the encryption at rest solution. This exercise often requires a network architect, database administrator, detailed mapping, and time.
Once encrypted, and assuming that long-string encryption such as AES 256 is utilized, the data is only secure right up to the point that it is needed. The data will eventually be needed to support a business function, such as customer service, sales, billing, financial service, healthcare, audit, and/or general update operations. At that point, the entire required dataset (whether the full database or a segment) needs to be decrypted and moved to a datastore as vulnerable plaintext.
This brings another layer of complexity—the expertise of a DBA or database expert, time to decrypt, the build out of a security enclave of complex solutions designed to monitor and “secure” the plaintext datastore. Now this enclave of complex solutions requires a specialized team of experts with knowledge of how each of those security tools function. Add in the need to patch and refresh each of those security tools just to maintain their effectiveness, and we now understand why so much data is compromised daily.
Of course, once the data set has been utilized, it’s supposed to be moved back to its encrypted state. So, the cycle of complexity (and expense) begins again.
Because of this cycle of complexity, in many situations, this sensitive data remains in a completely unencrypted, vulnerable state, so it is always readily available. 100% of threat actors agree that unencrypted data is the best kind of data for them to easily access.
This example focuses on encryption of data at rest, but it’s important to note that data encrypted in transit goes through much of the same process—it’s only encrypted in transit but needs to be decrypted for use on both ends of the transaction.
There is a much better approach. One that goes beyond baseline encryption. A modern, more complete database encryption strategy must account for encryption of critical database data in three states: at rest, in motion, and now IN USE. Searchable Encryption, also called Encryption-in-Use, keeps that data fully encrypted while it’s still usable. Removing the complexity and expense related to supporting an archaic encrypt, decrypt, use, re-encrypt process.
Merging Technologies for Better Encryption#
So why, now, is Searchable Encryption suddenly becoming a gold standard in critical private, sensitive, and controlled data security?
According to Gartner, “The need to protect data confidentiality and maintain data utility is a top concern for data analytics and privacy teams working with large amounts of data. The ability to encrypt data, and still process it securely is considered the holy grail of data protection.”
Previously, the possibility of data-in-use encryption revolved around the promise of Homomorphic Encryption (HE), which has notoriously slow performance, is really expensive, and requires an obscene amount of processing power. However, with the use of Searchable Symmetric Encryption technology, we can process “data in use” while it remains encrypted and maintain near real-time, millisecond query performance.
IDC Analyst Jennifer Glenn said, “Digital transformation has made data more portable and usable by every part of the business, while also leaving it more exposed. Searchable encryption offers a powerful way to keep data secure and private while unlocking its value.”
“Technologies like searchable encryption are rapidly becoming a staple for organizations to keep data usable, while ensuring its integrity and security,” Glenn said.
A 30+ year old data management company, Paperclip, has created a solution to achieve what was once referred to as the ‘holy grail of data protection’, encryption of data in use. By leveraging patented shredding technology used for data storage and Searchable Symmetric Encryption, a solution was born that removes the complexity, latency and risk inherent with legacy data security and encryption strategies.
The SAFE Encryption Solution#
Understanding that necessity is the mother of all inventions, Paperclip, founded in 1991 as a content supply-chain innovator, realized they themselves needed to do more to secure the cadre of sensitive data their client’s trusted them with. When analyzing the growing number of data breaches and data ransom attacks, one reality became abundantly clear: threat actors aren’t compromising or stealing encrypted data.
They are laser focused on the vast amounts of unencrypted, plaintext data being used to support key operational activities. That’s where they can do the most damage. That’s the best data to hold hostage. It was this critical data that needed to be addressed. It was time to evolve the way we encrypted our most active data, at the database layer.
This was the genesis of SAFE, first as a solution then to bring it to the commercial market.
Of course, identifying the challenge was easy. All organizations have sensitive data to protect, and all organizations have sensitive data they rely on to run their core operations. The next stage was to build a practical solution.
Paperclip SAFE is a SaaS solution that makes fully encrypted, searchable data encryption a practical reality. The entire process of encrypting, decrypting, using, re-encrypting—and the resources needed to accomplish those tasks— is no longer required. More importantly, SAFE removes the excuse related to why millions of records are left fully exposed to data theft and ransom attacks right now.
SAFE Searchable Encryption is commonly referred to as a Privacy Enhancing Technology (PET) Platform. As a PET, SAFE evolves the way data is secured at the core database layer. SAFE is unique to all other encryption solutions because it provides the following features:
- Full, AES 256 encryption supporting data owner and data holder key vaults – A threat actor must compromise both disparate keys. Even then they don’t get access to the data.
- Patented Paperclip Shredded Data Storage (SDS) – Even before any data is encrypted with AES 256, complex encryption, the data is shredded into pieces, salted and hashed. This breaks all context and creates entropy. Imagine a threat actor compromises both encryption keys. What they end up with is like taking a micro cross-cut shredder, running one million documents through it, throwing out a third of the shredded pieces, replacing that third with shredded old encyclopedias, shaking it up and throwing it on the floor like some sick, demented jigsaw puzzle. Based on current technology it will take about 6,000 years to reassemble all those pieces.
- Always Encrypted dataset supporting full create, read, update, delete (CRUD) functionality. – Inherently, when the data isn’t in use, it’s at rest, still fully encrypted. No more encrypted, unencrypted… It’s always encrypted.
- Fast encrypted compound searching (<100 milliseconds over a standard SQL query). End users won’t even realize that SAFE is running in the background.
- Continuous Machine Learning and AI Threat Detection and Response (TDR) – SAFE is based on Zero Trust so the solution will monitory and learn user trends. Any out-of-band activity will be blocked and will require administrative action. The solution is also monitoring for SQL injections, data fuzzing, and other threat actor actions. As part of the solution, SAFE produces a lot of telemetry that can feed a Client’s SOC monitoring service.
- Simple JSON API integration. There is some development involved, but the result is no disruption to the end user and a dataset of always available, always encrypted data.
- Implementation Flexibility – SAFE is a SaaS solution, but it was also designed to be implemented as a lightweight on-premises solution. In addition, SAFE can be integrated within a third-party application where that third-party is maintaining sensitive data on behalf of the Client (outsourced application like human resources, payroll, banking platforms, healthcare EMR & PHR, etc.). If you outsource your sensitive data to a third-party vendor, it’s time to ask how they’re encrypting that data. What happens if that vendor is breached? Is your data encrypted?
We’re in a race, one that the threat actors seem to be winning. It’s time to build a better encryption engine. It’s time for SAFE.
In today’s cyber-centric business landscape, the need for searchable encryption spans many industries and use cases such as Financial Services, Healthcare, Banking, Manufacturing, Government, Education, Critical Infrastructure, Retail, and Research to name a few. There isn’t an area where data doesn’t need to be more SAFE.
SAFE as a SaaS solution can be implemented in less than 30-days with no disruption to end users or network architecture. To learn more about SAFE searchable encryption, visit paperclip.com/safe.
Note: This article is expertly written and contributed by Chad F. Walter, Chief Revenue Officer at Paperclip since June 2022, leading Sales and Marketing initiatives, with over 20 years of experience in cybersecurity and technology.